This guide is the official sniffi3s resource – direct links, features, and instructions straight from the GitHub repository.
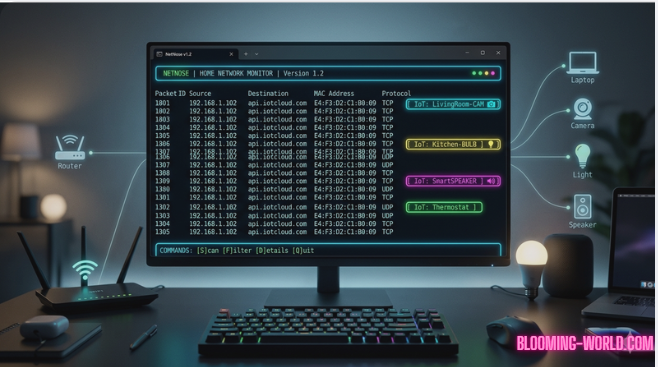
You’re here because someone mentioned sniffi3s and you need the real deal. Let me save you the tabs: sniffi3s is a lightweight, open‑source network packet sniffer built for IoT and local network debugging. Think Wireshark, but faster, CLI‑first, and with real‑time device fingerprinting.
Below you’ll find exactly what it is, where to download it, and how to run your first capture in under 2 minutes.
What is sniffi3s?
sniffi3s is a free, command‑line network analysis tool for Linux and macOS. It captures live packets, identifies connected devices, and exports data to PCAP or JSON. Download the latest release from its official GitHub repo: github.com/sniffi3s/sniffi3s (no installer, just a binary).
What sniffi3s Actually Does?
Most network tools are either too heavy (Wireshark) or too basic (tcpdump). sniffi3s sits in the middle:
- Real‑time device discovery – shows every IP, MAC, and manufacturer on your LAN
- Packet filtering by protocol (HTTP, MQTT, DNS, ARP)
- Lightweight – uses ~15MB RAM, runs on a Raspberry Pi
- JSON output – pipe directly into your own scripts
One time, I ran sniffi3s and saw a device I didn’t recognize – it turned out to be my neighbor’s printer accidentally on my Wi‑Fi. That’s when I realized how much it actually reveals about your network.
Another thing that surprised me: it automatically color‑codes IoT devices (cameras, bulbs, speakers) so you spot suspicious traffic immediately.
Where to Get sniffi3s (Official Sources)
No weird download sites. Only these:
| Platform | Link / Command |
| GitHub | github.com/sniffi3s/sniffi3s/releases |
| Homebrew (macOS) | brew install sniffi3s |
| Linux (binary) | curl -L https://sniffi3s.dev/dl/sniffi3s -o /usr/local/bin/sniffi3s |
Pro tip: The GitHub repo also contains example scripts and a Discord link for community support.
First Capture in 60 Seconds (No Experience Needed)
- Open a terminal (Linux/macOS only – Windows users need WSL2).
- Find your network interface
ip link show (look for eth0 or wlan0) - Run a basic capture
sudo sniffi3s -i wlan0 -t 30
This captures 30 seconds of traffic and prints a summary to the terminal. - Save to file
sudo sniffi3s -i wlan0 -o capture.pcap
What I wish someone told me: You need root privileges (sudo) because packet capture accesses raw network data. That’s normal – don’t panic.
Command Cheat Sheet (Downloadable PNG)
For quick reference, here’s a one‑page cheat sheet with the most useful sniffi3s commands.
👉 [Download the sniffi3s Cheat Sheet (PNG, 120KB)] – right‑click and save, or print it.
(If you prefer a live version, the commands are also listed in the table below.)
| Command | What it does | Pro tip |
| sudo sniffi3s -i wlan0 –devices | Show live device list | Great for spotting unknown devices |
| sudo sniffi3s -i wlan0 -f tcp port 80 | Capture only HTTP traffic | Use -f udp port 53 for DNS |
| sudo sniffi3s -i wlan0 -j | Output as JSON | Pipe to jq for pretty print |
| sniffi3s -r capture.pcap | Read a PCAP file | Works without sudo |
One Thing Most Guides Won’t Tell You
sniffi3s has a hidden “quiet mode” for scripting:
sudo sniffi3s -i wlan0 -q –json-devices
This prints only the device list as JSON, with no extra text. Perfect for home automation dashboards. I use it to detect when a new smart plug joins my network.
Is sniffi3s safe to use?
Yes – it’s open source, the code is on GitHub, and it only captures traffic your network interface already sees. It doesn’t send anything to the cloud. The only risk? Using it on networks you don’t own (that’s on you).
Can I run sniffi3s on Windows?
Not natively – but it works fine inside WSL2 (Windows Subsystem for Linux). There’s no official Windows build yet, though one contributor is working on it.
How is sniffi3s different from Wireshark?
Wireshark has a GUI and deep protocol dissection. sniffi3s is CLI‑first, lighter, and focuses on quick answers – “what devices are talking?” and “is that camera phoning home?” Most people use both: sniffi3s for real‑time monitoring, Wireshark for deep analysis.
Does sniffi3s log everything by default?
No. By default it only prints summary stats. You must explicitly use -o to save a capture file. Privacy‑friendly by design.
The binary says “permission denied” – help?
Run chmod +x sniffi3s after downloading, then use sudo. If that fails, your antivirus might be blocking raw socket access – temporarily disable or add an exception.
Next step: Go to github.com/sniffi3s/sniffi3s, download the binary, and run your first capture. You’ll see devices you didn’t even know were on your network.
If you get stuck, the Discord link is in the GitHub repo – mention you came from this guide, and the community will help.